Bl00dy Ransomware
Original Issue Date:-
June 12, 2023
Virus Type:- Ransomware
Severity:-
Medium
It has been reported that a ransomware known as "Bl00dy" is targeting organizations. The ransomware is majorly focussing on education sector. The attackers evade user authentication measures and gain unauthorized entry to the organization's server by assuming the role of administrators.
Infection Mechanism
The victims’ organizations are targeted by ransomware where the vulnerable PaperCut servers are exposed to the internet with CVE-2023-27350. As a result, data is leaked and the victims' systems are encrypted.
The Bl00dy ransomware attackers utilized the PaperCut vulnerability on port 9191 to initiate an initial network connection. The threat actors exploit the PaperCut NG vulnerability, specifically targeting port 9191, which led to the exposure of compromised organization information.
Once the threat actors gain access to the victim's systems, they proceed to steal data and encrypt the targeted systems. The attackers gain remote access to the devices by spawning new processes of 'cmd.exe' and 'powershell.exe' with elevated privileges. This allowed them to use the compromised devices as launch points for spreading laterally across the network.
The vulnerability also paves the way to deploy additional malicious payload for eg. Cobalt strike beacon to the compromised systems.
After infiltrating the victims' systems, the malicious actors modify the encrypted files by adding the ".DRTTY" extension. Additionally, a ransom note is placed in encrypted folders. The ransomware also eliminates shadow copies, further complicating the recovery process.
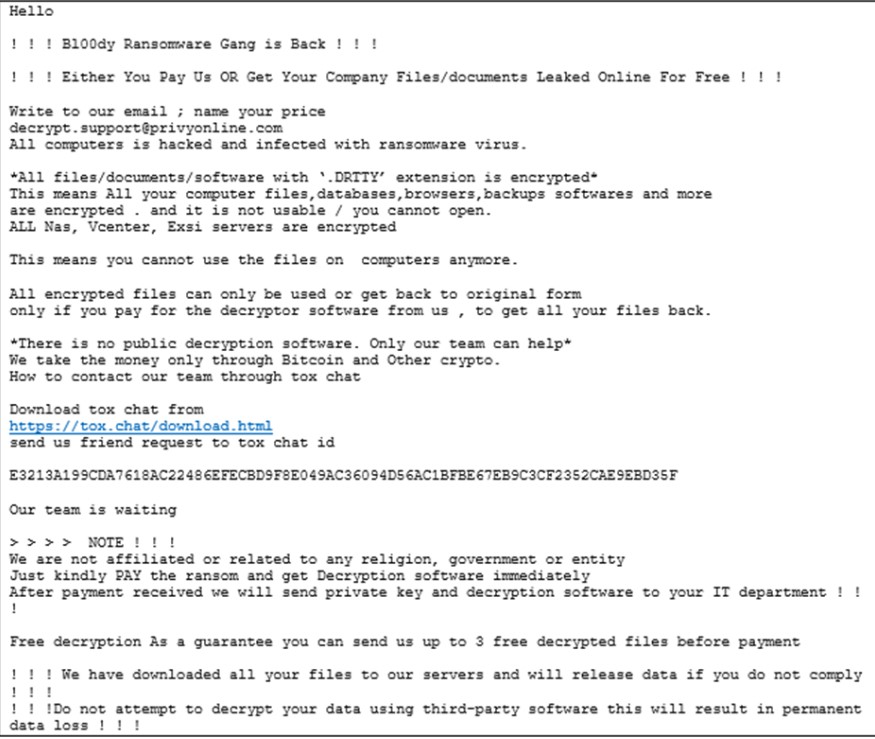
The ransom note mention about instructions for exchanging the decryption key, as well as information about the stolen data and communication and negotiation links. The Threat actors also utilize TOR to communicate with C2.
Indicator of Compromise:
Email:
- decrypt.support@privyonline[dot]com
- fimaribahundqf@gmx[dot]com
Domains:
- anydeskupdate[dot]com
- anydeskupdates[dot]com
Tox ID:
- E3213A199CDA7618AC22486EFECBD9F8E049AC36094D56AC1BFBE67EB9C3CF2352CAE9EBD35F
IP address:
- 102.130.112[dot]157
- 172.106.112[dot]46
For more detailed list of IoC, kindly refer the URL:
Best Practices and Recommendations:
- Option 1: Implement external controls by blocking all inbound traffic from external IP addresses to the web management portal (port 9191 and 9192 by default).
- Option 2: Implement both internal and external controls by blocking all inbound traffic to the web management portal. Please note that after implementing this step, remote management of the server will not be possible.
- Use RDP Gateways for better management.
- Change the listening port for Remote Desktop.
- Tunnel Remote Desktop connections through IPSec or SSH.
- Two-factor authentication may also be considered for highly critical systems.
References:
- https://blog.cyble.com/2023/05/30/bl00dy-ransomware-targets-indian-university-actively-exploiting-papercut-vulnerability/
- https://www.cisa.gov/news-events/cybersecurity-advisories/aa23-131a
- https://www.bleepingcomputer.com/news/security/fbi-bl00dy-ransomware-targets-education-orgs-in-papercut-attacks
- https://thehackernews.com/2023/05/bl00dy-ransomware-gang-strikes.html
- https://blog.cyble.com/2022/09/28/bl00dy-new-ransomware-strain-active-in-the-wild
- https://www.csk.gov.in/alerts/ransomware.html