Goldoson Android Malware
Original Issue Date:-
April 25, 2023
Virus Type:- Android Banking Trojan
Severity:-
Low
It has been reported that an android malware, dubbed “Goldoson” is affecting the official Google Play store's /Android’s applications through the malicious library, which belongs to a third party and utilized by developers in their application.
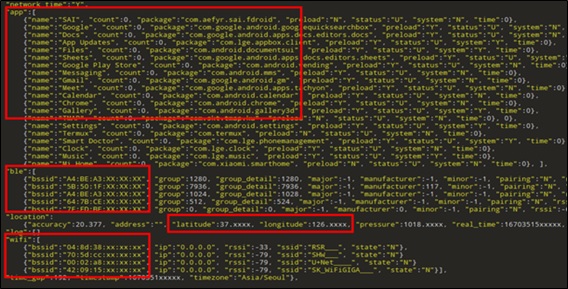
The malware is capable of collecting sensitive information from multiple applications. Once it infects the device, it would begin to collect sensitive data about installed applications and the history of Wi-Fi & Bluetooth connected devices, GPS location, etc.
It can also execute ad-fraud by clicking the advertisement for various web pages without the user's consent or knowledge.
Infection Mechanism
The Attacker gets access when the user works with the infected application after registration of the Goldoson library in the device.
It collects information and functions based on remote configuration parameters. Further, malicious library pulls the information according to set parameters and transmits them to the remote servers (C2 Server).
As observed, the collection of data depends on the permission granted to the infected application during installation. The sensitive information such as installed apps, location history, WiFi connected devices are siphoned off to attacker.
It also contains an ad-clicking operation through HTML code which loads the web pages in the background without user consent to increase the traffic on multiple URL visits for gaining profit.
The latest versions of Android i.e., Android 11 and above are more protected as compared to the lower versions of Android against the capricious data collection. However, some applications on recent versions of Android are also infected.
Indicator of Compromise:
Domains:- bhuroid[d0t]com
- enestcon[d0t]com
- htyyed[d0t]com
- discess[d0t]net
(Note: Replace “[d0t]” with “.” For actual domain.)
Package Name:- com.lottemembers.android
- com.Monthly23.SwipeBrickBreaker
- com.realbyteapps.moneymanagerfree
- com.skt.tmap.ku
For complete list of Domains & Packages, kindly refer the URL:
Best Practices and Recommendations:
- Reduce the risk of downloading potentially harmful apps by limiting your download sources to official app stores, such as your device’s manufacturer or operating system app store.
- Prior to downloading / installing apps on android devices (even from Google Play Store):
- Always review the app details, number of downloads, user reviews, comments and "ADDITIONAL INFORMATION" section.
- Verify app permissions and grant only those permissions which have relevant context for the app's purpose.
- Do not check "Untrusted Sources" checkbox to install side loaded apps.
- Install Android updates and patches as and when available from Android device vendors.
- Google Play Protect should be enabled on Android device.
- Permissions should also be given carefully.
- Do not browse un-trusted websites or follow un-trusted links and exercise caution while clicking on the link provided in any unsolicited emails and SMSs.
- Install and maintain updated anti-virus and antispyware software.
- Do extensive research before clicking on link provided in the message. There are many websites that allow anyone to run search based on a phone number and see any relatable information about whether or not a number is legit.
- Only click on URLs that clearly indicate the website domain. When in doubt, users can search for the organisation's website directly using search engines to ensure that the websites they visited are legitimate.
- Consider using Safe Browsing tools, filtering tools (antivirus and content-based filtering) in your antivirus, firewall, and filtering services.
- Exercise caution towards shortened URLs, such as those involving bit.ly and tinyurl. Users are advised to hover their cursors over the shortened URLs (if possible) to see the full website domain which they are visiting or use a URL checker that will allow the user to enter a short URL and view the full URL. Users can also use the shortening service preview feature to see a preview of the full URL.
- Look out for valid encryption certificates by checking for the green lock in the browser's address bar, before providing any sensitive information such as personal particulars or account login details.
- Customer should report any unusual activity in their account immediately to the respective bank with the relevant details for taking further appropriate actions.
References:
- https://www.mcafee.com/blogs/other-blogs/mcafee-labs/goldoson-privacy-invasive-and-clicker-android-adware-found-in-popular-apps-in-south-korea
- https://www.bleepingcomputer.com/news/security/android-malware-infiltrates-60-google-play-apps-with-100m-installs
- https://thehackernews.com/2023/04/goldoson-android-malware-infects-over.html
- https://gbhackers.com/android-malware-60-apps