RTM Locker ransomware
Original Issue Date:-
May 17, 2023
Virus Type:- Ransomware
Severity:-
Medium
It has been reported that a ransomware, dubbed “RTM Locker” has advanced capabilities which is targeting Linux and VMware ESXi platforms exclusively.
The threat actors behind the malware operates as ransomware-as-a-service (RaaS) provider and infuse it with the capabilities to infect Linux, NAS, and ESXi hosts etc. The ransomware encrypts critical data, files, documents etc. and threaten the victim to public the sensitive details while asking for ransom payment.
Infection Mechanism
Virtual Machines/ ESXi platform are increasingly being implemented in enterprise environment because of their advanced capabilities and ease of access. The RTM locker ransomware focusses on VMware ESXi servers for attack as observed in the current trend, initial infection vector of the malware is still unknown.
RTM group created the Linux encryptors using asymmetric and symmetric encryption techniques which makes it difficult to mitigate the attack and to decrypt all these files as it require attacker's private key. The malware’s encryption algorithm is statically compiled in binary code making it more efficient and difficult to reverse engineer.
During infection, the encryptor first gather the list of all active VMs before staring encryption then it terminates all active VMs. Before encrypting the files, it terminates the antivirus and backup and deletes shadow copies for making recovery difficult.
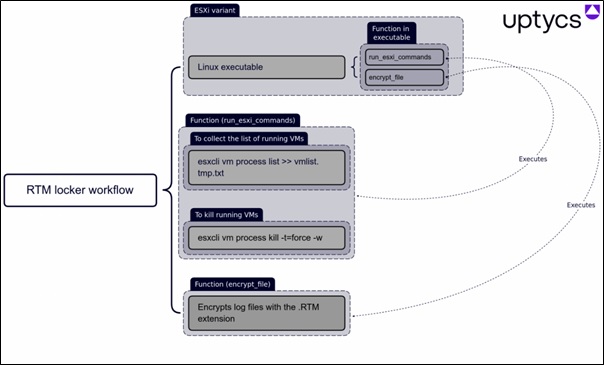
Once all the active VMs are terminated, the encryptor starts to encrypt the files that are related to VMs on ESXi host with the following extension: - .vmem (virtual machine memory), .vmsn (VM snapshots), .vmdk (virtual disks), .vswp (swap files), and .log (log files).
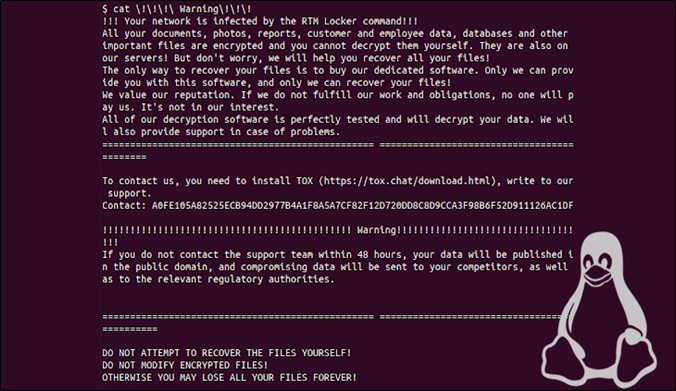
During encrypting files, the encryptor appends the .RTM file extension to encrypted file's names, and after it's done, creates ransom note named "Warning" on the infected system.
In this warning, the threat actors ask to contact RTM support via TOX for ransom payment and warn the victims of leaking the data on public domain.
It has also the capability to change the screen wallpaper, empty the recycle bin, wipe event logs and execute the shell command that self-deletes the locker.
Indicator of Compromise:
SHA 256:
- 55b85e76abb172536c64a8f6cf4101f943ea826042826759ded4ce46adc00638
- b376d511fb69085b1d28b62be846d049629079f4f4f826fd0f46df26378e398b
- d68c99d7680bf6a4644770edfe338b8d0591dfe143278412d5ed62848ffc99e0
Best Practices and Recommendations:
- Maintain offline backups of data, and regularly maintain backup and restoration. This practice will ensure the organization will not be severely interrupted, have irretrievable data.
- Ensure all backup data is encrypted, immutable (i.e., cannot be altered or deleted) and covers the entire organization’s data infrastructure.
- Enable protected files in the Windows Operating System to prevent unauthorized changes to critical files.
- Implement all accounts with password logins (e.g., service account, admin accounts, and domain admin accounts) to have strong, unique passwords.
- Implement multi-factor authentication for all services to the extent possible, particularly for webmail, virtual private networks, and accounts that access critical systems.
- Remove unnecessary access to administrative shares.
- Use a host-based firewall to only allow connections to administrative shares via server message block (SMB) from a limited set of administrator machines.
- Don't open attachments in unsolicited e-mails, even if they come from people in your contact list, and never click on a URL contained in an unsolicited e-mail, even if the link seems benign. In cases of genuine URLs close out the e-mail and go to the organization's website directly through browser.
- Disable remote Desktop Connections, employ least-privileged accounts. Limit users who can log in using Remote Desktop, set an account lockout policy. Ensure proper RDP logging and configuration.
- Check regularly for the integrity of the information stored in the databases.
- Ensure integrity of the codes /scripts being used in database, authentication and sensitive system.
- Establish Domain-based Message Authentication, Reporting, and Conformance (DMARC), Domain Keys Identified Mail (DKIM) and Sender Policy Framework (SPF) for your domain, which is an email validation system designed to prevent spam by detecting email spoofing by which most of the ransomware samples successfully reaches the corporate email boxes.
- Keep the operating system, third party applications (MS office, browsers, browser Plugins) up-to-date with the latest patches.
- Application white listing/Strict implementation of Software Restriction Policies (SRP) to block binaries running from %APPDATA% and %TEMP% paths. Ransomware sample drops and executes generally from these locations.
- Maintain updated Antivirus software on all systems.
- Follow safe practices when browsing the web. Ensure the web browsers are secured enough with appropriate content controls.
- Network segmentation and segregation into security zones - help protect sensitive information and critical services. Separate administrative network from business processes with physical controls and Virtual Local Area Networks.
- Disable ActiveX content in Microsoft Office applications such as Word, Excel, etc.
- Restrict access using firewalls and allow only to selected remote endpoints, VPN may also be used with dedicated pool for RDP access.
- Use strong authentication protocol, such as Network Level Authentication (NLA) in Windows.
- Additional Security measures that may be considered are:
- Use RDP Gateways for better management.
- Change the listening port for Remote Desktop.
- Tunnel Remote Desktop connections through IPSec or SSH.
- Two-factor authentication may also be considered for highly critical systems.
- If not required consider disabling PowerShell / windows script hosting.
- Restrict users' abilities (permissions) to install and run unwanted software applications.
- Enable personal firewalls on workstations.
- Implement strict External Device (USB drive) usage policy.
- Employ data-at-rest and data-in-transit encryption.
- Consider installing Enhanced Mitigation Experience Toolkit, or similar host-level anti-exploitation tools.
- Block the attachments of file types, exe|pif|tmp|url|vb|vbe|scr|reg|cer|pst|cmd|com|bat|dll|dat|hlp|hta|js|wsf
- Carry out vulnerability Assessment and Penetration Testing (VAPT) and information security audit of critical networks/systems, especially database servers from CERT-IN empanelled auditors. Repeat audits at regular intervals.
- Individuals or organizations are not encouraged to pay the ransom, as this does not guarantee files will be released. Report such instances of fraud to CERT-In and Law Enforcement agencies.
References:
- https://www.uptycs.com/blog/rtm-locker-ransomware-as-a-service-raas-linux
- https://thehackernews.com/2023/04/rtm-lockers-first-linux-ransomware.html
- https://www.bleepingcomputer.com/news/security/linux-version-of-rtm-locker-ransomware-targets-vmware-esxi-servers
- https://techmonitor.ai/technology/cybersecurity/rtm-sells-ransomware-targeting-linux
- https://www.csk.gov.in/alerts/ransomware.html