SecuriDropper
Original Issue Date:- November 17, 2023
Virus Type:- Dropper-as-a-Service (DaaS)
Severity:- High
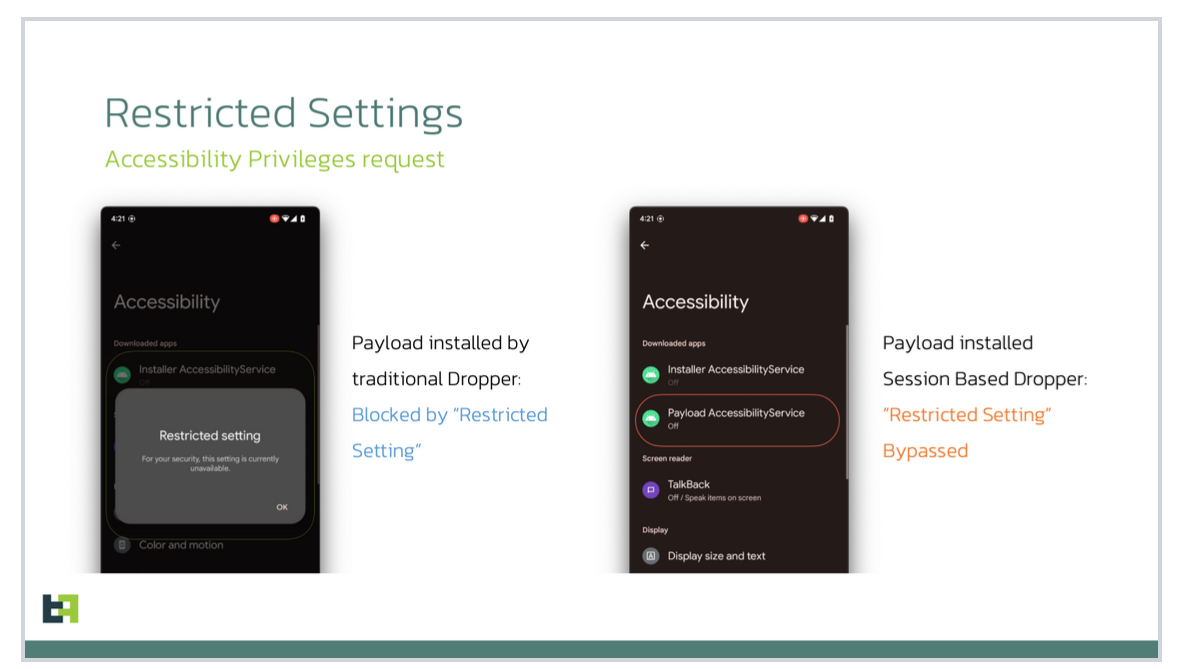
It has been reported that newly discovered Dropper-as-a-Service (DaaS), called SecuriDropper can bypass Android's security solutions including Android 13's Restricted Settings that prevents side-loaded applications (APK files) installed from outside Google Play. It disguises itself as a legitimate app and utilizing a 'session-based' installer, sideloads malware by mimicking the marketplace's installation process. SecuriDropper is a two-stage infection process, wherein the dropper installs a secondary payload belonging to malware categories of spyware or banking Trojans on devices.
Infection Mechanism:
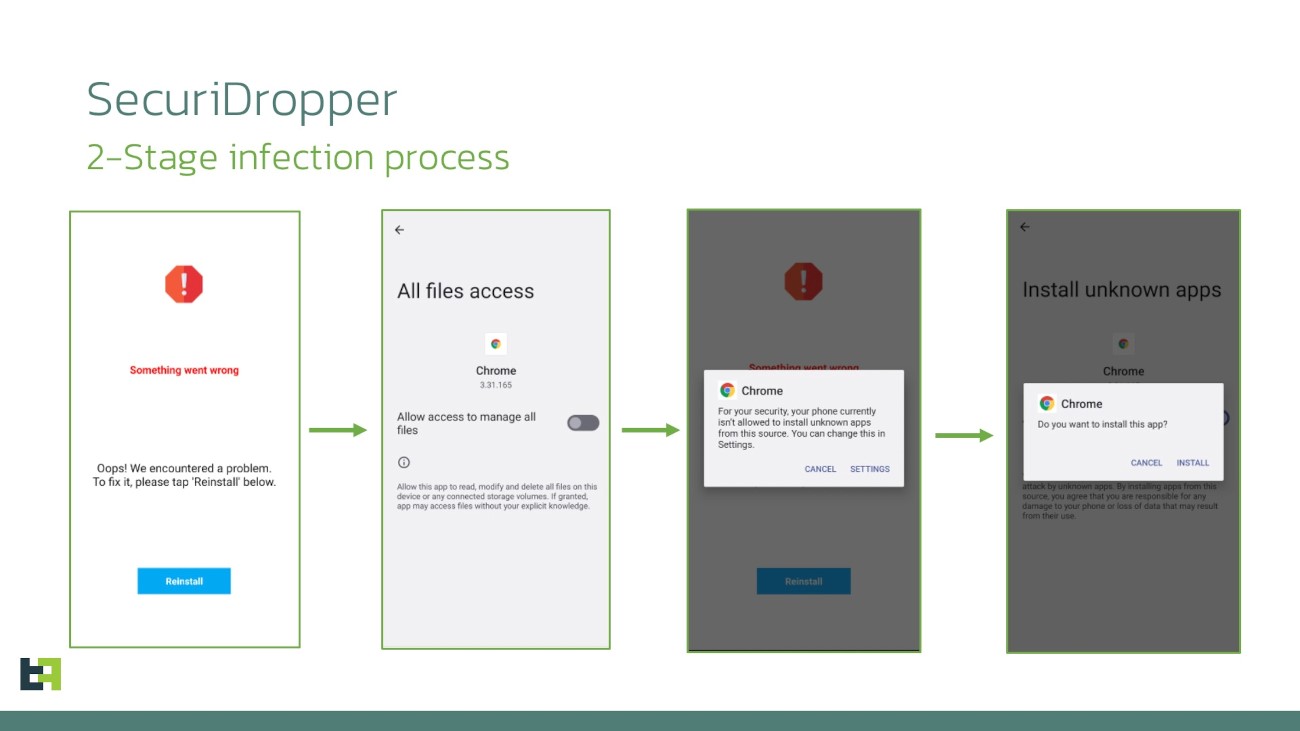
SecuriDropper, a Dropper-as-a-Service (DaaS), follows a two-step process to infect devices. It starts by spreading a harmless-looking app that pretends to be a legitimate app. This legitimate looking app, known as the dropper, is responsible for secretly installing a more harmful program like spyware or banking Trojans.
Phase 1: Dropper Installation
- SecuriDropper is disguised as a legitimate app and is sideloaded onto the device by mimicking the marketplace's installation process.
- Once installed, the dropper prompts the user for critical permissions such as "Read & Write External Storage" and "Install & Delete Packages."
- Once the permissions are granted, the dropper checks for the payload on the device.
- If the payload is not found, the dropper dynamically manages interfaces, presenting messages tailored to the device's language and location, prompting users to install the payload by clicking the "Reinstall" button.
- Once the user clicks "Reinstall," the dropper downloads the payload from a remote server and installs it on the device.
Phase 2: Secondary Payload Installation
- Once the payload is installed, the dropper launches it and hands over execution control.
- The payload then performs its malicious activities, such as stealing personal information or financial data."
Examples of SecuriDropper payloads:
- Spyware: "com.appd.instll.load (Google)"
- Banking Trojans: "com.appd.instll.load (Google Chrome)"
Indicators of Compromise
- FileHash-SHA256
- 68234450d90668909697893a76fc4a0791b35ba3f7bfc4d9d14f2866706019f3
- 2f64dd679494bdfba962bdc8ec6fb5e13ec4c754f12d494291442dc3e4862a93
- 22630eee4fdf1958e6c98721f0ccc522b2413a6f6c49f315f34c45726bf18b2d
- 13daf7b94124c142d509b036516eb3d532c22696574d8cd5d65aa9d636c293a9
- FileHash-SHA1
- b49e5fb5a5e4a04767561c01076589bbfca694f2
- 87180128deffce412bdbf0abbe279f2f52744efc
- 5a71760ed376618ca3563180af8a425787a3d950
- 6b56ac6c609f59914919cb379dde43e926c33059
- FileHash-MD5
- fe93e65c75e5f99b1f39f875aa923440
- 321550b738d3089f0ea5166b1363b540
- 5392abb157bcdffd49f578e71595b311
- 1a98e8eb0ed340101ba979fe8ccbe471
Best Practices and Recommendations:
- Reduce the risk of downloading potentially harmful apps by limiting your download sources to official app stores, such as your device’s manufacturer or operating system app store.
- Prior to downloading / installing apps on android devices (even from Google Play Store):
- Always review the app details, number of downloads, user reviews, comments and "ADDITIONAL INFORMATION" section.
- Verify app permissions and grant only those permissions which have relevant context for the app's purpose.
- Do not check "Untrusted Sources" checkbox to install side loaded apps.
- Install Android updates and patches as and when available from Android device vendors.
- Do not browse un-trusted websites or follow un-trusted links and exercise caution while clicking on the link provided in any unsolicited emails and SMSs.
- Install and maintain updated anti-virus and antispyware software.
- Be cautious when considering sideloaded apps obtained from unofficial sources. While sideloading offers access to a wider range of apps, it also presents security risks. Ensure you trust the source and origin of sideloaded apps
- Do extensive research before clicking on link provided in the message. There are many websites that allow anyone to run search based on a phone number and see any relatable information about whether or not a number is legit.
- Only click on URLs that clearly indicate the website domain. When in doubt, users can search for the organisation's website directly using search engines to ensure that the websites they visited are legitimate
- Consider using Safe Browsing tools, filtering tools (antivirus and content-based filtering) in your antivirus, firewall, and filtering services.
- Exercise caution towards shortened URLs, such as those involving bit.ly and tinyurl. Users are advised to hover their cursors over the shortened URLs (if possible) to see the full website domain which they are visiting or use a URL checker that will allow the user to enter a short URL and view the full URL. Users can also use the shortening service preview feature to see a preview of the full URL.
- Look out for valid encryption certificates by checking for the green lock in the browser's address bar, before providing any sensitive information such as personal particulars or account login details.
- Customer should report any unusual activity in their account immediately to the respective bank with the relevant details for taking further appropriate actions.
May like to visit the website of "Cyber Swachhta Kendra" (CSK) (https://www.csk.gov.in/security-tools.html) to download the Free Bot Removal Tools for Android viz. eScan CERT-In Bot Removal application and M-Kavach 2 application for identifying/detecting malicious/dangerous apps with high level permissions, installed on end user devices.
References: